
What is MEV
MEV stands for Maximal Extractable Value, referring to the additional profit extracted during block production by inserting or reordering transactions within a block.
The concept of MEV was first introduced in a paper titled ☞ Flash Boys 2.0: Frontrunning, Transaction Reordering, and Consensus Instability in Decentralized Exchanges (Philip Daian, Steven Goldfeder, et al., 2019). The paper defined MEV as Miner-extractable Value, representing the extra value miners could extract through transaction ordering rules.
The shift from Miner-extractable Value to Maximal Extractable Value reflects the evolution of MEV, where extractors expanded from solely miners to multiple participants, and extraction methods became more diverse. From the rise of decentralized exchanges based on the AMM model in 2021 to Ethereum’s full transition to Proof-of-Stake (PoS) in September 2022, MEV has undergone several key milestones. During this period, participants collaborated and competed, collectively shaping the MEV ecosystem.
Why Does MEV Exist
Transaction Ordering Based on Value
In blockchain systems, to prevent excessive consumption of node resources, block computation space is typically constrained by gas. The number of transactions a block can accommodate is limited. For block producers (miners), a transaction’s value is measured by its gas fee. By prioritizing high-gas-fee transactions through ordering algorithms, block producers maximize block revenue and enhance the blockchain network’s processing efficiency.
In BSC’s block production process, transaction inclusion and ordering were initially determined by Validators. After the implementation of the PBS (Proposer-Builder Separation) mechanism, this role shifted to Builders. Despite the change in roles, gas price remain the primary factor in transaction ordering algorithms.
Since transactions are executed sequentially within a block, earlier execution increases a user’s chance of securing their desired transaction outcome. During periods of on-chain congestion, users compete for limited block space by setting high gas fees to ensure their transactions are included and prioritized in the block.
For users, gas fees purchase priority execution rights; for block producers, including high-gas-fee transactions boosts block revenue. This value-based transaction ordering behavior between block producers and users forms the foundation of the MEV ecosystem.
Transaction Visibility
In BSC’s default implementation, transactions initiated by clients are broadcast across the P2P node network and remain visible while awaiting inclusion in a block. Anyone running a node or subscribing to transaction data can view pending transactions.
Transaction visibility creates another opportunity for MEV extraction. Beyond block producers, another role emerges: Searchers. Searchers leverage publicly visible transactions to extract MEV through strategies like arbitrage and liquidation. Upon detecting MEV opportunities, they construct strategic transactions, bundle them with user transactions, and submit them to block producers. With technological and informational advantages, Searchers extract strategy-based MEV while helping block producers further increase block revenue beyond gas fees.
Malicious MEV: The True Dark Forest
The metaphor of MEV as a "dark forest" was first articulated by Paradigm researchers Dan Robinson and Georgios Konstantopoulos in a 2020 blog post titled ☞ Ethereum is a Dark Forest. The article likened MEV competition to a predatory forest where arbitrage bots, front-runners, miners, and other participants engage in covert games, with ordinary users often unknowingly "preyed upon."
MEV itself is an objective phenomenon. Participants leverage technical, informational, or financial advantages to extract MEV in various ways, impacting user transaction experiences positively or negatively. This article categorizes MEV into malicious MEV, neutral MEV, and benevolent MEV, with malicious MEV—causing negative impacts—being the true "dark forest" that requires governance.
Malicious MEV
Malicious MEV is extracted at the expense of user interests and is the primary culprit lurking in the dark forest, necessitating robust countermeasures. Examples include sandwich attacks and front-running, with sandwich attacks having the most significant impact on user assets, particularly targeting swap transactions.
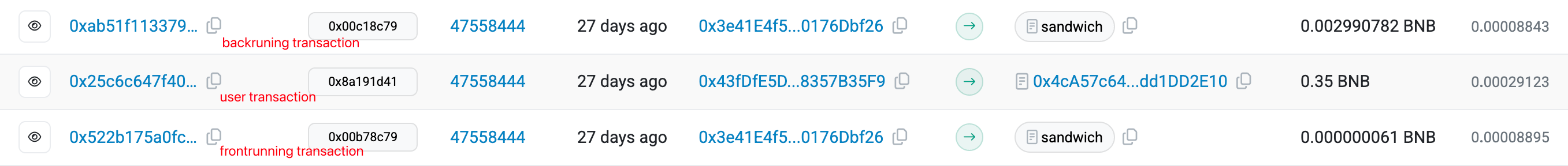
As shown in the above, an attacker detects a transaction (0x25) swapping WBNB for BabyTTAI on PancakeSwap. They insert a transaction (0x52) before 0x25, swapping in the same direction to inflate BabyTTAI’s price, forcing the user to swap at the slippage limit. Then, after 0x25, they insert a reverse swap transaction (0xab) to sell BabyTTAI at the inflated price back to WBNB. The attacker profits from buying low and selling high, while the user incurs slippage losses.


As shown, the attacker pays 0.064507401173204992 WBNB in the front-running transaction and recovers 0.067691499714772992 WBNB in the back-running transaction, netting a profit of 0.00318409854 WBNB.
Neutral MEV
Neutral MEV incentivizes participants to improve the ecosystem and can be divided into two categories:
Block Producers: Enhancing Infrastructure
As mentioned, block producers sort transactions by gas fees, extracting MEV while preventing spam transactions from wasting block space. This ensures efficient allocation of computational resources, reduces transaction congestion, and improves network efficiency. MEV serves as additional block production revenue, incentivizing block producers to make sustained contributions to the blockchain network.
Atomic/Non-Atomic Arbitrage: Strengthening DeFi Ecosystems
Atomic and non-atomic arbitrage strategies capitalize on price discrepancies for the same asset across exchanges, eliminating inconsistencies and reducing transaction costs due to price differences. These strategies also inject liquidity into markets, mitigating sharp price fluctuations and promoting stability.
Benevolent MEV
In contrast to malicious MEV, benevolent MEV protects user interests. Initiators of benevolent MEV can counteract hackers by inserting rescue transactions before or after malicious attacks, helping users avoid asset losses.
After a Hacker’s Transaction
Upon detecting a hacker’s transaction, benevolent MEV initiators can execute a rescue transaction immediately afterward to recover user losses. On July 22, 2024, a benevolent MEV initiator successfully rescued $2,000 worth of staked assets from a user’s compromised wallet. See details at ☞ https://x.com/0xAA_Science/status/1815067523299361029.
Before a Hacker’s Transaction
When vulnerabilities in DeFi protocols are detected, predicting potential hacker attacks, benevolent MEV initiators can execute white-hat front-running transactions to transfer funds to secure addresses preemptively.
On March 17, 2023, Paraspace (now Parallel Finance) suffered a hacker attack due to a price oracle vulnerability, attempting to steal 2,900 ETH (~$5 million). The attack failed as BlockSec’s Phalcon Block system detected it in real-time, enabling white-hat hackers to replicate the attack, seize control of the assets, and return 2,900 ETH to Paraspace. See details at ☞ https://x.com/BlockSecTeam/status/1636621097495044096.
On July 30, 2023, Curve reported that stablecoin pools (alETH/msETH/pETH) using Vyper 0.2.15 were attacked due to a Vyper bug. Alchemix preemptively transferred 12,980 alETH to a team multisig wallet via white-hat actions for later compensation to affected liquidity providers. See details at ☞ https://x.com/AlchemixFi/status/1685737632133971968.
How BSC MEV Operates
The MEV ecosystem involves users, block producers, and Searchers. To enhance this ecosystem, BSC implemented the PBS mechanism in 2024 based on ☞ BEP-322, separating block producers into Validators and Builders. Users, Builders, Validators, and Searchers collectively form BSC’s MEV ecosystem, with a transaction’s journey from initiation to inclusion reflecting their collaborative roles in the MEV supply chain.
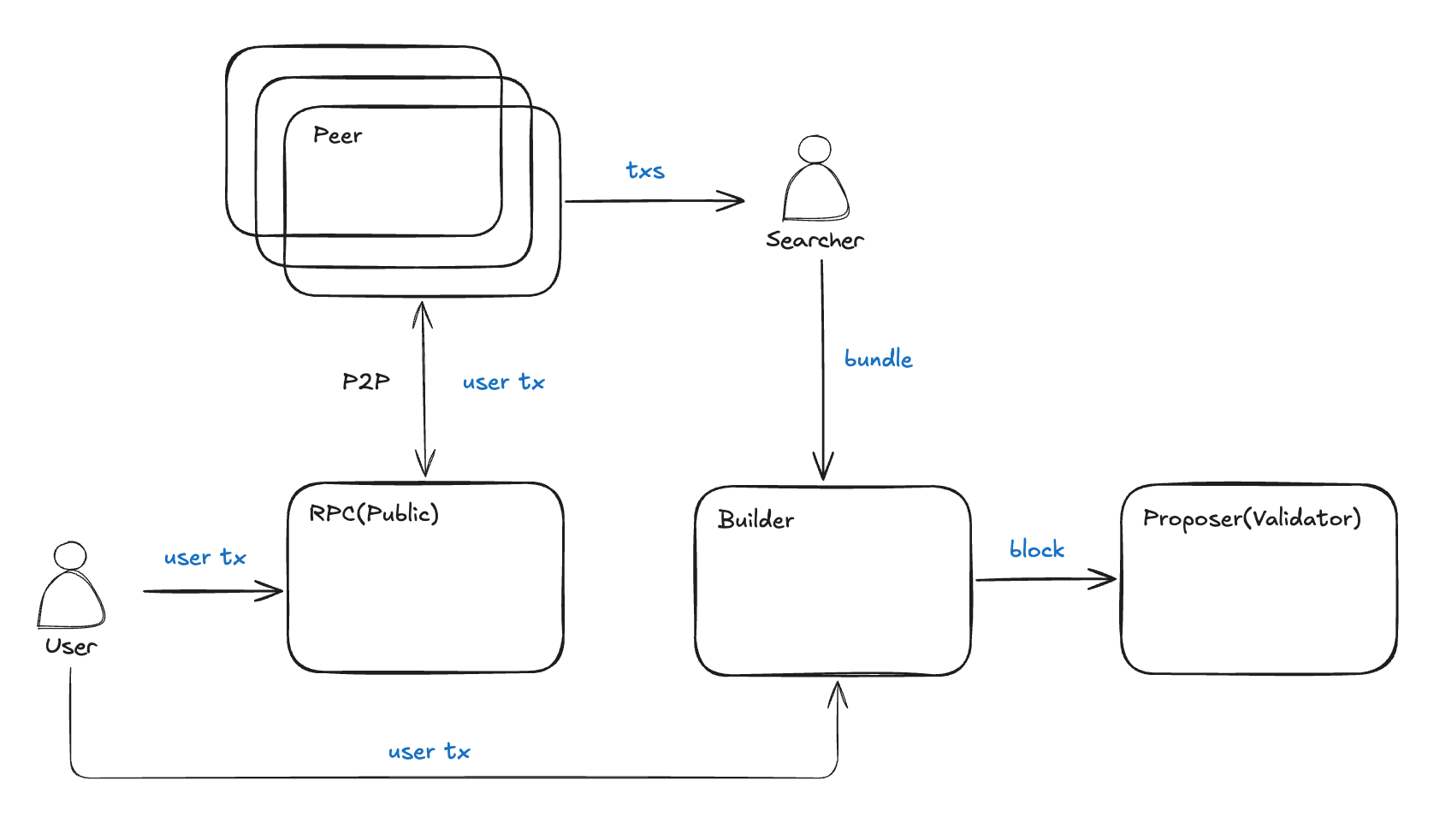
The process of a transaction from initiation to inclusion in the MEV supply chain is as follows:
- A user initiates a transaction via a wallet or DApp.
- The transaction is submitted to an RPC, verified for correctness, and broadcast to the P2P network, awaiting inclusion.
- Searchers monitor MEV signals, construct MEV transactions, and submit them to Builders, either individually or as bundles (sets of transactions executed in a specific order).
- Builders receive bundles and transactions, package them into the highest-value block using transaction ordering algorithms, and submit it to the Proposer (elected from Validators).
- The Proposer selects the highest-value block from multiple Builders, synchronizing it to Validators for verification and execution.
In this MEV supply chain:
- RPCs receives and verifies orderflow from wallets, decentralized exchanges, etc.
- Builder receives private transactions to ensure transaction security and bundles to guarantee the atomic execution of strategic transactions. Simultaneously, it packages the received transactions into the most valuable block and submits it to the Proposer.
- The Proposer (Validator) is the ultimate entity determining the transaction order and the final link in the MEV supply chain, with most MEV flowing to Validators from upstream participants (users, Searchers, and Builders).
The Past and Future of BSC MEV
BSC’s PBS mechanism, implemented in 2024, introduced specialization and competition in block production, optimizing MEV extraction and distribution while reducing centralization risks. Post-PBS, BSC’s MEV ecosystem continues to evolve.
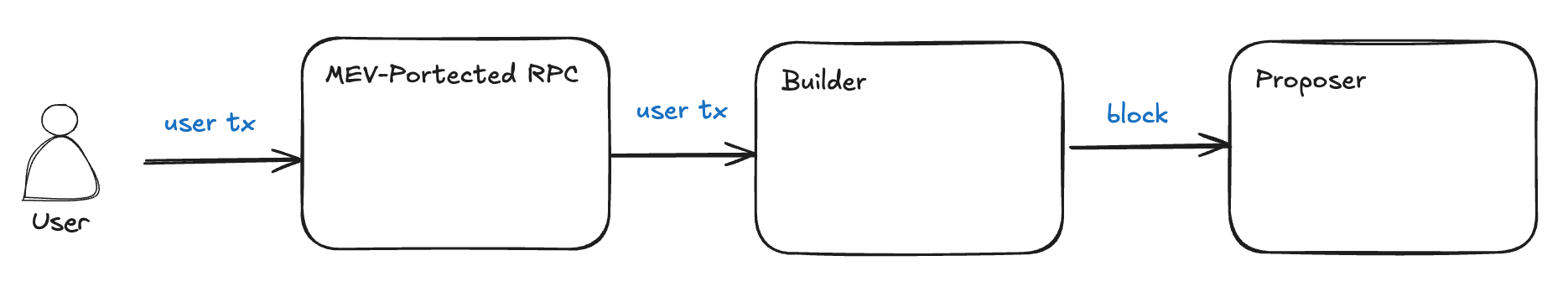
MEV-Protect RPC
To ensure transaction flow privacy for wallets and decentralized exchanges, and to prevent transactions from being exposed to public P2P networks and sandwich attacks, MEV-protect solutions like Scutum RPC and 48Club RPC were launched on BSC in October 2024. Transactions submitted to MEV-protect RPCs bypass public P2P networks, going directly to Builders to shield against malicious MEV attacks.
Goodwill Alliance
While MEV-protect RPCs mitigated malicious MEV on BSC, the issue persisted. In March 2025, the BNB Chain team and community core members formed the BNB Goodwill Alliance, with its first initiative aimed at further reducing sandwich attacks.
Key MEV supply chain players like BlockRazor and 48Club responded by deploying sandwich filters to detect and block such attacks in real-time. Validators, following the team’s call, only accepted blocks from Builders with sandwich filtering capabilities. Through the Goodwill Alliance’s efforts, malicious MEV was further curbed.
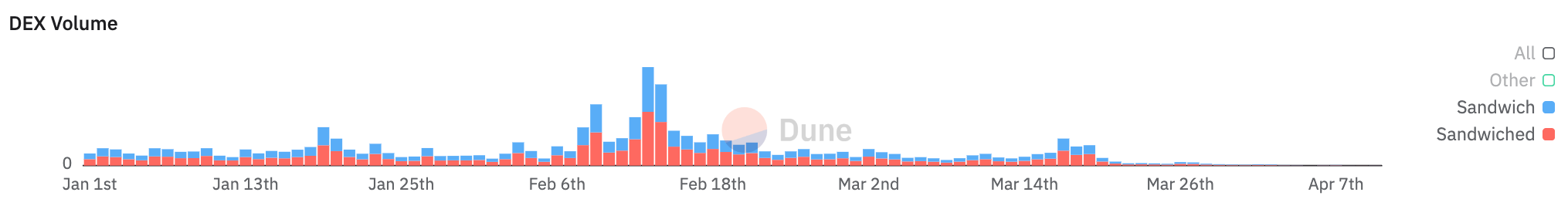
As shown, since the Goodwill Alliance’s formation on March 18, 2025, DEX transaction volumes tied to sandwich attacks have significantly declined. See ☞ https://dune.com/hildobby/sandwiches?Blockchain_e8f77a=bnb
Future Outlook
Governing malicious MEV on BSC remains a long-term challenge. While sandwich attacks are being filtered, attackers are exploring other malicious methods like non-atomic sandwiches and front-running. Continuous research into MEV attack-defense dynamics is the Goodwill Alliance’s top priority. Improving user transaction experiences during network congestion via the MEV supply chain is another critical area. We will continue to conduct data observation and research to contribute to the ecological development of BSC MEV.
Conclusion
BSC’s MEV ecosystem currently involves users, RPCs, Builders, Validators, and Searchers. In the MEV supply chain, users acting as transaction originators are at a disadvantage due to limited technical expertise, information, and capital. They fail to obtain the expected experience and may even face malicious MEV attacks. This article argues that orderflow is the foundation of MEV value distribution and that MEV should be harnessed to enhance their transaction experience.
BlockRazor’s Scutum MEV-protect RPC embodies this philosophy, prioritizing user experience and striving for equitable MEV distribution. BlockRazor plans to roll out additional products and services, collaborating with MEV supply chain participants to refine BSC’s MEV ecosystem.
Malicious MEV remains a significant pain point for users. BlockRazor will publish an article on the evolution of sandwich attack-defense strategies, and interested users can follow updates on ☞ X to build a theoretical foundation for transaction security.